OverTheWire Wargame "Natas" Level 0 [How-To/Web]
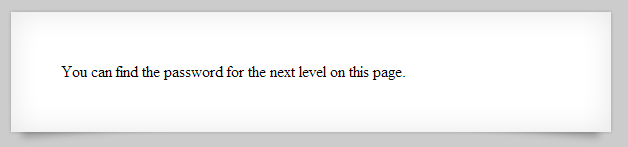
OverTheWire has released a new WarGame called "Natas" which focuses on web security, so I thought I'd try my hand at it and give some walkthroughs/how-tos as I beat each level. I'm still a newbie at websec, so deal with me! Going to the front page of Natas , it gives us the creds to get into level 0, so we need to find level 1's creds somehow.