Anonymous browsing with Tor [Windows/Linux/Firefox/Chrome]
Anonymity online is one of the most important rights users have today and is a right we are slowly losing due to bills and laws being passed in governments worldwide, especially in the United States.
Bills like SOPA/PIPA/ACTA and other unconstitutional and unlawful proposals are everywhere and the Internet is standing up against them, with massive sites like Wikipedia and Reddit blacking out their services to bring awareness.
If these are passed, everyday Internet interaction would change forever. For those who have visited China or know of the "Great Firewall" are appalled that any government would want to do this to their citizens and freedom, but alas, governments always want more power and money, and this is the way to it.
Well, enough of the political preaching, lets get into how to by-pass these "Great Firewalls" and other proxy settings to have anonymity on the Internet! Just a note though, it is impossible in this day and age to achieve perfect anonymity. At least one node, person, or organization other than yourself knows who you are and what you view. Using the methods here to conduct illegal activities will not make you safe, you WILL GET CAUGHT eventually, especially if you do it often enough. I'm writing this how-to and informational piece for those constricted by governments or any other blocking method that removes the freedom to the Internet, so again... do not conduct illegal activities without accepting the consequences (which will come).
The biggest proxy service used in today's age is TOR, or The Onion Router. TOR was created to provide anonymity online for anyone. Their main page is located at: https://www.torproject.org/ where you can read up more on them, but I'll be telling you how to install TOR for your needs on Windows and Linux computers.
Installing TOR on Windows (XP-Vista-7)
Now, installing Tor is quite easy. First, go to this website and click the "Download" large orange button. It's 20.4mbs, so it should only take a few seconds to download. After it's done, run the .exe by double clicking it or single clicking it in the download bar if you're using Chrome.
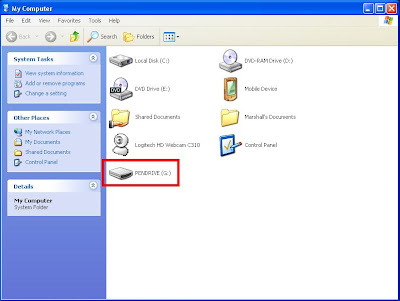
After running the executable, an extraction location will appear. Whatever the default is should be fine. Remember this location. Mine was my downloads folder (where I originally downloaded it to). Just click "Extract" and let it do its work, this should take a minute or so.
When its done extracting, move to that directory and in there should be a folder called "Tor Browser" with everything in it. Yeah, that was easy, right? You can move this folder to where ever you want to "install" Tor to, but it's about 84mb so in this day and age anywhere is really fine. Let's explore what goodies are in the folder now!
In the "app" folder are all the .dll files necessary for Tor to run.
In the "data" folder are most of the configuration files.
In the "docs" folder are read-mes and open-source licenses.
In the "FirefoxPortable" folder is the portable version of Firefox that Vidalia (a vidalia is a type of onion, by the way) uses.
Finally there's the .exe "Start Tor Browser," go ahead and double click that and let Tor load up its GUI (graphical user interface).
This is Tor's GUI called Vidalia. When you loaded it up, there should have been a bar where the "connected to the tor network" is with information about it connecting and authenticating. Also, when you load up Vidalia, it automatically opens the portable Firefox up already connected. Let's test this out and review it.
If you take a look at the Firefox homepage, it's the check website to see if you're using Tor (how useful!).
Mine looks like this:
As you can see, it tells me my IP address... but wait... that's not my REAL IP address! It's a proxied IP address to somewhere in the world! If you want to check it against yours, open a command prompt (Start menu -> run -> "cmd" then type "ipconfig /all" and look for your "IPv4 Address"
Note: if you're behind a router, this will be a private address (192.168.x.x). We'll talk about private addressing in another post soon. If you want an alternative to see your real IP address, open up a new browser with Tor not enabled and go to whatismyip.com and it will tell you your REAL IP address.
As you can see, the last two octets (an octet is 8 bits, I will make a post about subnetting and binary later for you guys!) are different than the last two in my Tor IP address.
Going back to the main menu for Vidalia. The "stop tor" button is quite obvious in what it does (it stops tor!), so I cannot really expound upon that any further.
There are a few cool things here if you want to explore them. For instance, the "view the network" button gives you an amazing look at the connections going on in the Tor network including their IP addresses, their bandwidth, time up, and other interesting facts. It gives points on the map of where they are located and you can zoom in on them.
The "setup relaying" button is used if you wish to become a forwarding node for the Tor network. If you live in a country outside the United States, I highly suggest looking into your local and federal laws to see if you will receive any problems, and if possible, become a node. Here's the main link to get you started: Relay Configuration.
The "use a new identity" button refreshes who you are connecting to and updates your IP address. Useful if you want to update your "location" every little while to retain more anonymity.
The bandwidth graph shows your input/output on the Tor network and is useful to see which nodes have faster connections and the sort.
The message log is not very useful to the average user, but may come in handy if you need to use it.
The settings are used if you wish to start Vidalia and the Tor service on start (it's off by default), or update your relaying status, but the settings can all stay default for the average user.
The exit button closes your Tor connection and the Firefox window associated with it, so don't close the Firefox or Vidalia unless you want to close the other one as well.
Well, this was a quick write-up for now, I'm going to add in the Linux section as soon as I get dual-booting working on my Dell XPS 15 (there's a large issue with the BIOS and dual-installing, but I should have it fixed soon) and I'll add in the details to how an Onion network runs and other cool things.
Bills like SOPA/PIPA/ACTA and other unconstitutional and unlawful proposals are everywhere and the Internet is standing up against them, with massive sites like Wikipedia and Reddit blacking out their services to bring awareness.
If these are passed, everyday Internet interaction would change forever. For those who have visited China or know of the "Great Firewall" are appalled that any government would want to do this to their citizens and freedom, but alas, governments always want more power and money, and this is the way to it.
Well, enough of the political preaching, lets get into how to by-pass these "Great Firewalls" and other proxy settings to have anonymity on the Internet! Just a note though, it is impossible in this day and age to achieve perfect anonymity. At least one node, person, or organization other than yourself knows who you are and what you view. Using the methods here to conduct illegal activities will not make you safe, you WILL GET CAUGHT eventually, especially if you do it often enough. I'm writing this how-to and informational piece for those constricted by governments or any other blocking method that removes the freedom to the Internet, so again... do not conduct illegal activities without accepting the consequences (which will come).
The biggest proxy service used in today's age is TOR, or The Onion Router. TOR was created to provide anonymity online for anyone. Their main page is located at: https://www.torproject.org/ where you can read up more on them, but I'll be telling you how to install TOR for your needs on Windows and Linux computers.
Installing TOR on Windows (XP-Vista-7)
Now, installing Tor is quite easy. First, go to this website and click the "Download" large orange button. It's 20.4mbs, so it should only take a few seconds to download. After it's done, run the .exe by double clicking it or single clicking it in the download bar if you're using Chrome.
| Click the orange "Download" button and run the .exe |
When its done extracting, move to that directory and in there should be a folder called "Tor Browser" with everything in it. Yeah, that was easy, right? You can move this folder to where ever you want to "install" Tor to, but it's about 84mb so in this day and age anywhere is really fine. Let's explore what goodies are in the folder now!
In the "app" folder are all the .dll files necessary for Tor to run.
In the "data" folder are most of the configuration files.
In the "docs" folder are read-mes and open-source licenses.
In the "FirefoxPortable" folder is the portable version of Firefox that Vidalia (a vidalia is a type of onion, by the way) uses.
Finally there's the .exe "Start Tor Browser," go ahead and double click that and let Tor load up its GUI (graphical user interface).
| Vidalia |
If you take a look at the Firefox homepage, it's the check website to see if you're using Tor (how useful!).
Mine looks like this:
As you can see, it tells me my IP address... but wait... that's not my REAL IP address! It's a proxied IP address to somewhere in the world! If you want to check it against yours, open a command prompt (Start menu -> run -> "cmd" then type "ipconfig /all" and look for your "IPv4 Address"
Note: if you're behind a router, this will be a private address (192.168.x.x). We'll talk about private addressing in another post soon. If you want an alternative to see your real IP address, open up a new browser with Tor not enabled and go to whatismyip.com and it will tell you your REAL IP address.
 |
| Too lazy to open Photoshop to blur! |
Going back to the main menu for Vidalia. The "stop tor" button is quite obvious in what it does (it stops tor!), so I cannot really expound upon that any further.
There are a few cool things here if you want to explore them. For instance, the "view the network" button gives you an amazing look at the connections going on in the Tor network including their IP addresses, their bandwidth, time up, and other interesting facts. It gives points on the map of where they are located and you can zoom in on them.
The "setup relaying" button is used if you wish to become a forwarding node for the Tor network. If you live in a country outside the United States, I highly suggest looking into your local and federal laws to see if you will receive any problems, and if possible, become a node. Here's the main link to get you started: Relay Configuration.
The "use a new identity" button refreshes who you are connecting to and updates your IP address. Useful if you want to update your "location" every little while to retain more anonymity.
The bandwidth graph shows your input/output on the Tor network and is useful to see which nodes have faster connections and the sort.
The message log is not very useful to the average user, but may come in handy if you need to use it.
The settings are used if you wish to start Vidalia and the Tor service on start (it's off by default), or update your relaying status, but the settings can all stay default for the average user.
The exit button closes your Tor connection and the Firefox window associated with it, so don't close the Firefox or Vidalia unless you want to close the other one as well.
Well, this was a quick write-up for now, I'm going to add in the Linux section as soon as I get dual-booting working on my Dell XPS 15 (there's a large issue with the BIOS and dual-installing, but I should have it fixed soon) and I'll add in the details to how an Onion network runs and other cool things.